Get updates from Network Box USA
Enter your email address to receive news and insights from us.
All latest news
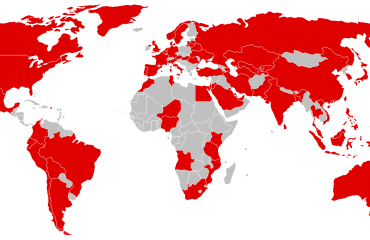
Thriving in the Era of Cyberattacks
When we say cybersecurity, we immediately think hackers, spam, phishing, rogue nations, Nigerian scams, and the likes. Our mind automatically …
Old Passwords for Sale: May Still Work
Last week, Troy Hunt, a security researcher who runs Have I Been Pwned, reported finding an 87GB file of 773M …
When Does Security Become Too Much?
Is there even such a thing as too much cyber security? And can it be counterproductive? In my opinion the …
Healthcare, Compliance, and Email Security
Email, without question, is the most efficient way to communicate information quickly and accurately. However, transmitting confidential patient data electronically …
Predicting 2019
Every year, come rain or shine, when the month of December rolls around, someone will inevitably ask me, “What do …
What’s the Deal with Ransomware Today?
We last talked about ransomware a while back when 2016 was dubbed as the year of ransomware. Since then, there …
How I Protect My Personal Data From Cyber Threats
I’ve resisted writing for the blog for almost six years now, for the simple reason that I simply did not …
Top Cloud Security Threats – Part 2
Last week, we looked at 5 of the top cloud security threats. This week, we continue the list, as well …
Top Cloud Security Threats – Part 1
When it comes to adopting and moving to the cloud, security is often cited as one of the top concerns, …