Keep Fighting The Phish
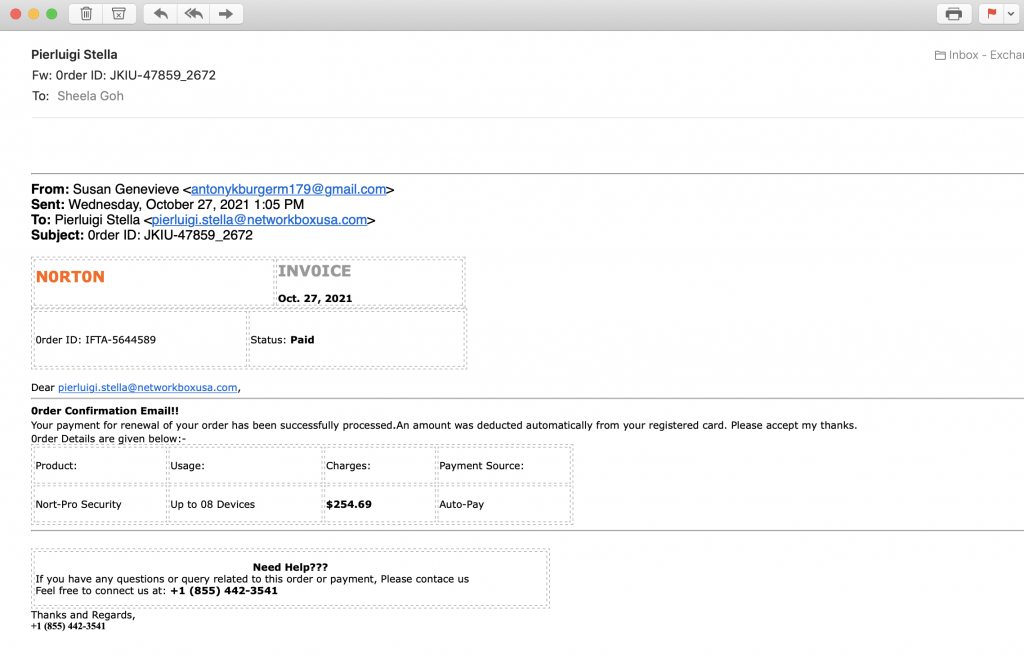
Look at the above. It’s a screenshot of an email I received a little while ago – proof that we must never let our guard down when it comes to phishing emails, and that we simply must keep fighting the phish.
Yes, it’s a new form of phishing.
There are no links. No questions asked. No requests for information. Just text. But very enticing text if you’re a Norton client. I mean, they’re claiming your renewal will be charged (and soon) for $254.00. The amount is large enough that most people will question and possibly call. And when they call, if they’re not careful, they could very easily be tricked into giving scammers access to their computers.
This precise thing happened to an employee of a client of ours recently. Scammers convinced her to give them remote access to her computer, and in her situation, attempted access was via Teamviewer. However, as the Network Box blocked that particular doorway, scammers were unable to execute their (obviously nefarious) plan. But the fact remains that they were convincing and the user fell for it. And someone might fall for this email too. When you call, they do answer that phone number. Trust me on this because I called, and I verified. And essentially, the number’s active, and there’s someone waiting to answer the phone.
So what’s going on here?
In the past, phishing used to be an email purporting to be from your bank, leading you to a website which will look exactly like that of your bank. But those emails are easy to block for decent antispam systems. Therefore, hackers need to find a way to bypass every technology defense in place, and access the one singular part of our network they know is easy to manipulate.
The user.
Nowadays, phishing scams almost all follow similar lines of thinking.
The email contains nothing that an email filter might be able to recognize as dangerous. Name of sender changes for every email, even phone numbers are recycled frequently meaning that too is hard to blacklist (we do still blacklist them as fast as we can). And thanks to all these, the email seems legitimate enough that someone might be enticed to call, worrying about being charged a hefty $254. Of course, the call per se isn’t dangerous, but if the user is naive then that call could end up with the scammer logged onto the user’s computer, with complete access to bank accounts, logins, and every morsel of valuable personal information they can get their greedy hands on.
Scammers are undeniably creative.
But they all share one common trait – the constant search for ways to trick our end users, who are (and will always remain) the weakest link in our security chain. And the only way to strengthen that link is to continue to educate them. Every time we see something new, like this email above, we need to alert our users and point out how to spot a scam like this. To keep them always on the alert and ensure they’re aware of the existence of such possible attacks.
They are, after all, our last line of defense.