SIEM: The One Log Monitoring & Management Tool You Need In Your Cybersecurity Arsenal
A quick question for the cybersecurity decision-makers. How do you want your cybersecurity software to be defined? Agile? Durable? Intelligent? They’re all important considerations. However, the function of a cybersecurity infrastructure extends beyond identifying and countering security threats. It must be more than just something that identifies threats and throws them out of the infrastructure with its tail between its legs. It needs to also encompass security logging and monitoring. Both of these being integral to maintaining a robust cybersecurity infrastructure. Which brings us to today’s article. What is the one log monitoring and management tool you need in your cybersecurity arsenal right now?
Think about it.
Numerous devices, systems, and applications are currently running on your network. And every single one of them is generating logs that need to be monitored and analyzed.
Hiring someone to mull over each log is time-consuming and inefficient. Your time is valuable.
How do you take care of this?
You get a SIEM.
What’s a SIEM?
A SIEM is a log management tool that can help you handle this influx of logs.
Traditionally, SIEM stands for “security information and event management“. Here at Network Box USA, however, we prefer to call it “security incident and event management” because it’s about more than just information.
What does a SIEM do?
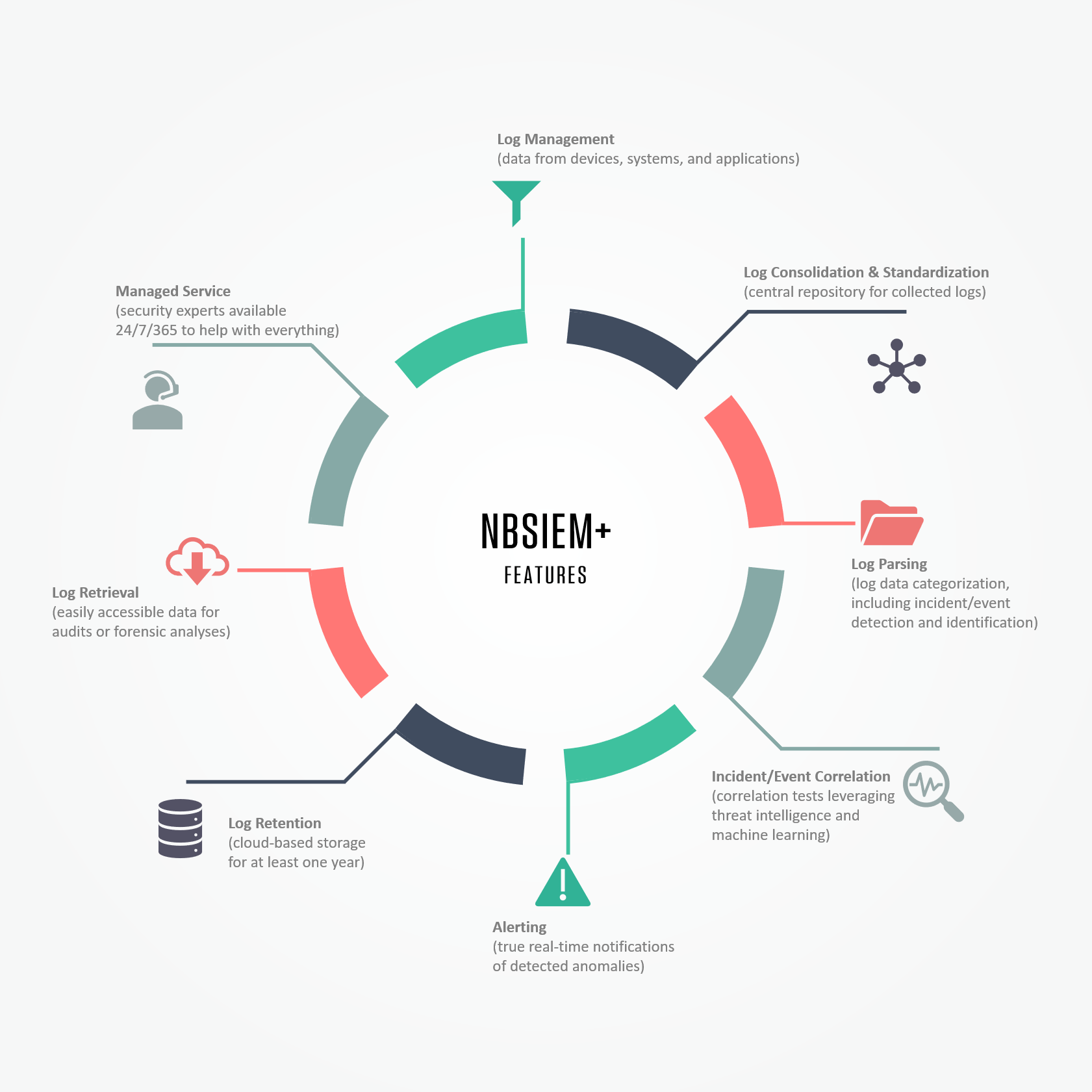
A SIEM collects and consolidates logs from every device, system, and application in your network. It then scans those logs to detect anomalies. Leveraging threat intelligence and machine learning, it runs correlation tests to identify any potential threats. Once it identifies a threat, a SIEM will alert you in real-time. That way, you can take appropriate action. And swiftly.
For instance, let’s say unauthorized activities (or attempts thereof) are found. This data is then moved to a central database for additional investigations and necessary steps. In a time where digital threats are widespread and ever-changing, the data gleaned from these log files is absolutely vital in keeping your infrastructure agile and responsive.
Learn more about the Network Box SIEM (NBSIEM+).